The technical coaching periods at Black Hat USA provide a novel monitoring alternative, as they ship hands-on studying alternatives for attendees to try new assaults. Many coaching periods use a cloud useful resource owned by the coach that the attendees connect with immediately from the coaching room. This creates a visitors path of finish customers connecting to a wi-fi entry level (AP) that’s routed alongside an inspected visitors path out to the cloud. Our position within the SOC throughout the Black Hat NOC is to make sure secure connectivity for the AP and visitors path to the web, and to observe to confirm that the assault visitors popping out of the school rooms is destined for the authorised coaching assets, and isn’t launched towards different targets.
We had a number of conventional intrusion guidelines hearth for assault coaching visitors, and as we noticed in Black Hat Asia in Singapore, SnortML (quick for Snort Machine Studying) supplied one other layer of detection that picked up assaults that didn’t all the time match our conventional ruleset. Most impressively, the constancy of SnortML alerts was very excessive—with over 29 TB of wi-fi knowledge on the convention, we solely had two recurring false positives from SnortML occasions, with over 100 assaults precisely recognized. The total occasion breakdown seems to be like this:
- 29.8 TB of community visitors
- 133 SnortML occasions
- Over 100 true positives
- 21 false positives associated to Chocolatey (a software program administration program)
- 8 false positives associated to Microsoft downloads
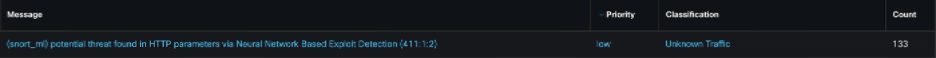
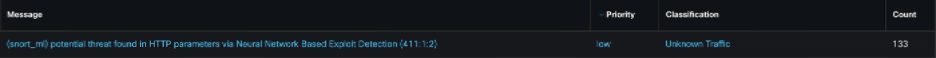
As anybody who has carried out evaluation of intrusion occasions can attest, coping with excessive false optimistic charges is without doubt one of the largest challenges. Having an occasion set with such a excessive fee of true positives (over 75%) was an enormous profit.
SnortML False Positives
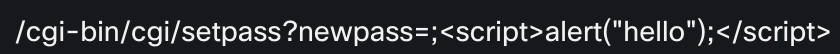
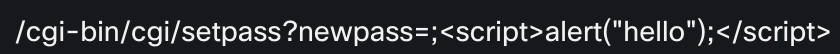
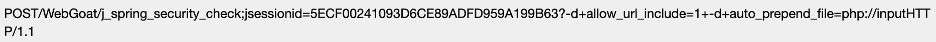
What tripped up SnortML at Black Hat? The primary false optimistic was a really lengthy string associated to a Microsoft file obtain.


The tip of the above string in a bigger font:


Specifically the %3dpercent3d (which decodes to ==) on the finish stood out as encoding that probably tripped the detection. The opposite string that generated false positives was associated to Chocolatey (put in your studying glasses):
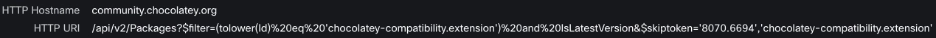
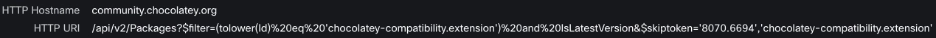
Decoding the above yields the next output:


Whereas this isn’t malicious, it has a number of traits that look an terrible lot like SQL injection, together with very beneficiant use of single quotes. The command ‘tolower’ is one other factor that the mannequin additionally noticed as prone to be associated to malicious exercise.
Whereas each of the above are false positives, it’s comprehensible that SnortML flagged them as malicious, significantly Chocolatey. Our SOC at Black Hat introduced within the lead developer for SnortML to overview the occasions in order that the SnortML fashions will be tuned to keep away from these false positives.
SnortML True Positives
SnortML at the moment has detection fashions for each SQL injection and Command Injection, with extra fashions deliberate for future software program releases. We noticed many alternative assault permutations for these two occasion sorts at Black Hat. SnortML additionally proved very correct at detecting path traversals and makes an attempt to entry delicate recordsdata, equivalent to /and so forth/passwd and /and so forth/hosts. The screenshot beneath exhibits the payloads from a set of SnortML occasions, with the alerting packets downloaded into Wireshark.


The above are true positives assaults but in addition acceptable for the Black Hat community—all of them originated from technical coaching rooms and have been focused at assets owned by the trainers.
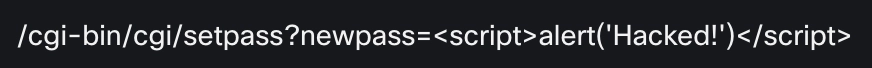
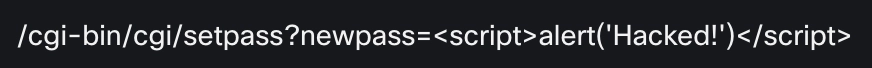
SnortML additionally picked up a number of flavors of command injection, starting from college students experimenting with script strings like ‘hi there’ and ‘Hacked!’ to injecting instructions like ‘Whoami’ and ‘ls’.




Safety Instruments Detected by SnortML
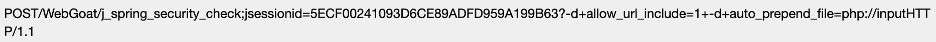
Given that every one of Black Hat’s technical trainings concerned safety ultimately, it wasn’t stunning to see a number of instruments pop up, together with the well-known WebGoat insecure server and a ‘notsosecureapp’ web site dedicated to instructing cyber safety. Beneath is a full occasion screenshot displaying path a traversal try and the notsosecureapp server.


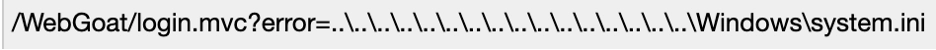
We noticed a number of occasions involving WebGoattogether with path traversals that launched encoding.


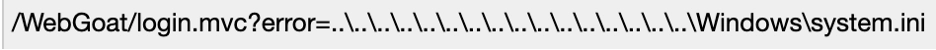
And makes an attempt to traverse delicate Home windows recordsdata.


The above decodes to the next:
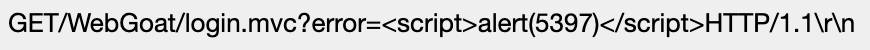
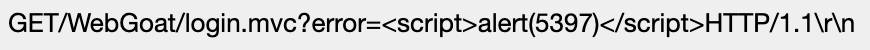
Different WebGoat assaults included makes an attempt to insert scripts utilizing fundamental command injection.
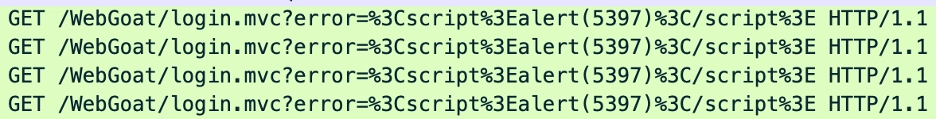
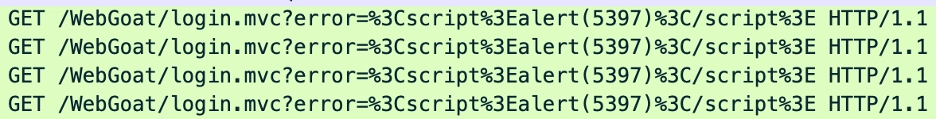
The above decodes to a easy command injection that causes an alert popup.
Extra superior assaults have been additionally captured:


The above decodes to:


Injecting the sleep command will be a straightforward technique to verify a profitable assault, as it should lead to a delay of the returned webpage (for the interval specified) whether it is profitable and the sleep command isn’t run by a background course of.
SnortML additionally picked up a number of makes an attempt to insert recordsdata:
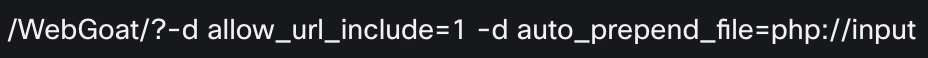
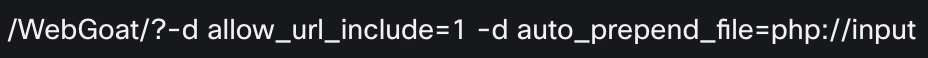


The above decodes to:
Closing Ideas
SnortML isn’t a alternative for a strong intrusion ruleset—our conventional ruleset picked up essential assaults that SnortML isn’t skilled to detect, together with inbound assaults towards public going through Black Hat servers that tried to take advantage of current CVEs. Nonetheless, the unbelievable accuracy of SnortML at Black Hat 2025—over 75% true optimistic fee—made it a particularly helpful and high-fidelity complement to our conventional intrusion rule set. We stay up for rolling out new detection fashions for SnortML at future conferences.
About Black Hat
Black Hat is the cybersecurity business’s most established and in-depth safety occasion collection. Based in 1997, these annual, multi-day occasions present attendees with the most recent in cybersecurity analysis, improvement, and developments. Pushed by the wants of the group, Black Hat occasions showcase content material immediately from the group by way of Briefings shows, Trainings programs, Summits, and extra. Because the occasion collection the place all profession ranges and tutorial disciplines convene to collaborate, community, and talk about the cybersecurity subjects that matter most to them, attendees can discover Black Hat occasions in the US, Canada, Europe, Center East and Africa, and Asia. For extra info, please go to the Black Hat web site.
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media
Share:

