Segmentation has emerged as a foundational know-how for cybersecurity groups around the globe as a approach to cease threats from spreading laterally by way of the community, mitigate their influence and implement zero belief methods. Dozens of segmentation options have flooded {the marketplace} – all claiming one of the best strategy for defining, figuring out and isolating particular workloads based mostly on habits and identification.
The evolution of segmentation has been swift – dizzying even. And prospects are having bother breaking by way of the hype. What’s the finest segmentation strategy for my group? What resolution finest matches our wants? How can we measure and consider our segmentation technique? And the way does segmentation align with enterprise targets?
Because of this, we’re launching a brand new weblog sequence particularly centered on segmentation. Over the subsequent a number of months, we’ll discover use circumstances, challenges and techniques so you’ll be able to evaluate, deploy and handle segmentation options extra successfully throughout your various IT environments. We would like you to make knowledgeable choices – choices that improve total safety posture, help more and more complicated compliance efforts and improve zero-trust safety fashions.
Segmentation is Evolving to Meet Safety Challenges within the AI World
Segmentation was developed a long time in the past as a approach to implement visitors administration and forestall threats from transferring laterally throughout the community. Since then, as digital transformation, distributed computing and the cloud have modified the way in which we work, segmentation has developed to permit safety groups to isolate particular workloads based mostly on habits or identification.
This skill to implement micro-segmentation at scale has develop into foundational to fashionable enterprise safety methods and the zero belief safety mannequin – enabling the containment of breaches, the enforcement of entry insurance policies and improved visibility throughout more and more complicated IT environments and menace panorama.
That is very true within the age of AI. As we speak’s extremely subtle threats can unfold laterally throughout the community in a matter of seconds, and static segmentation insurance policies are unable to reply shortly to evolving threats. New AI-powered micro-segmentation options can pace response instances immensely. Safety groups have taken discover, embracing these micro-segmentation instruments to cease assaults earlier than they can unfold all through the community.
A Communication Drawback for Distributors, Integrators and Clients
The evolution of segmentation has created an unlimited ecosystem of assorted applied sciences, strategies, infrastructures and enforcement methods – contributing to a lot confusion within the market. Distributors and integrators use completely different phrases, push completely different approaches and make conflicting guarantees. The ensuing incapacity to totally grasp the subtleties of segmentation prevents organizations from having fruitful conversations round segmentation wants, challenges and options – finally placing segmentation initiatives prone to failure or not realizing their full worth.
As cybersecurity threats proceed to develop in quantity, sophistication and influence, organizations are going to want to get a greater grasp of this foundational know-how to allow them to make higher choices consistent with enterprise targets and danger.
Let’s Agree on a Customary Taxonomy for Segmentation
Step one is to standardize how we discuss segmentation. A current paper revealed at TechRxiv takes a primary stab at defining a typical taxonomy. Written by a Cisco colleague, the paper “introduces a taxonomy and shared vocabulary for discussing and evaluating segmentation approaches throughout real-world deployment contexts.”
Talking the identical language is vital as a result of it ensures that each one stakeholders are in settlement about what’s being mentioned and the way it’s being mentioned. When somebody makes use of a label, they’re assuming their subjective interpretation is identical because the viewers’s interpretation. If they don’t align, miscommunication can happen, resulting in confusion, disconnected expectations and, typically, harm emotions. Customary taxonomies be certain that everybody is talking the identical language, communication is clear and everyone seems to be aligned.
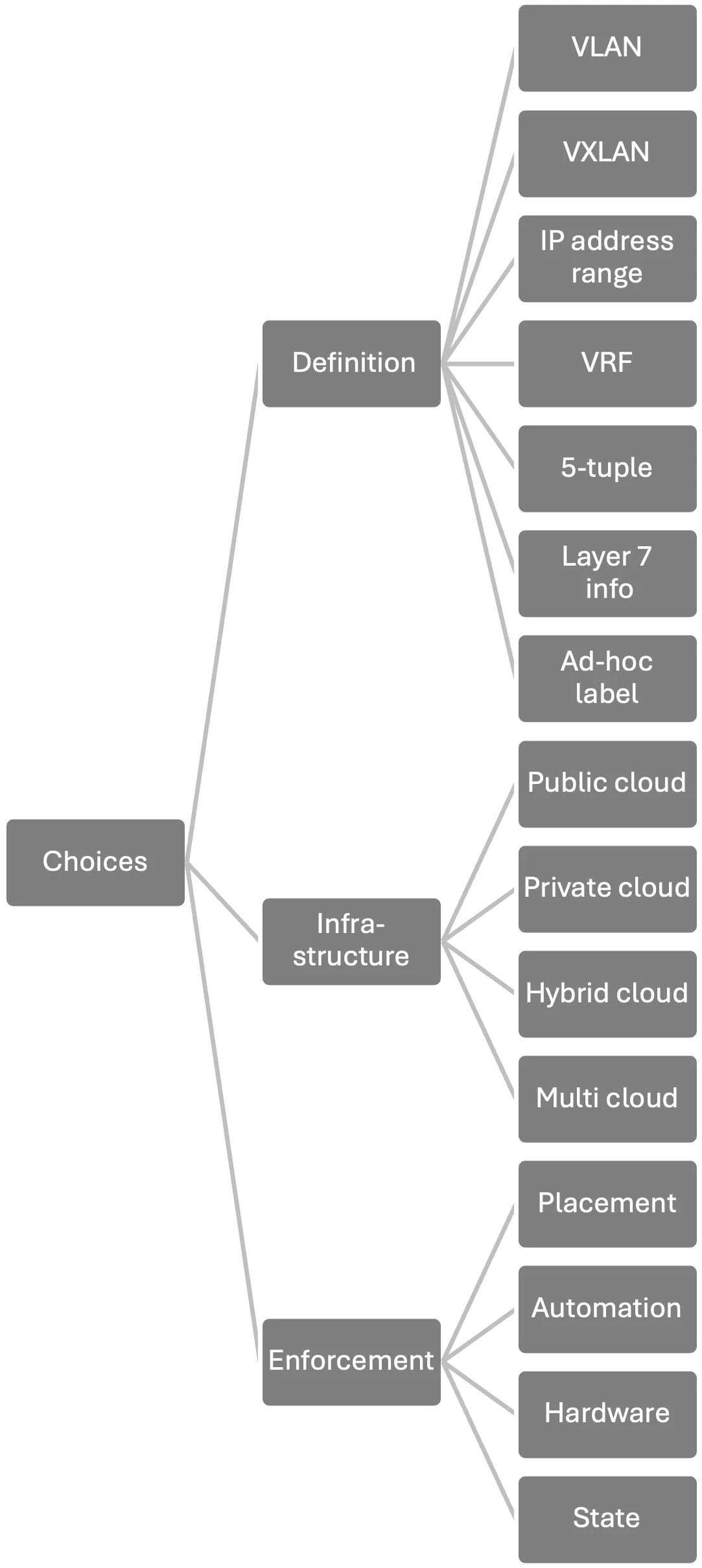
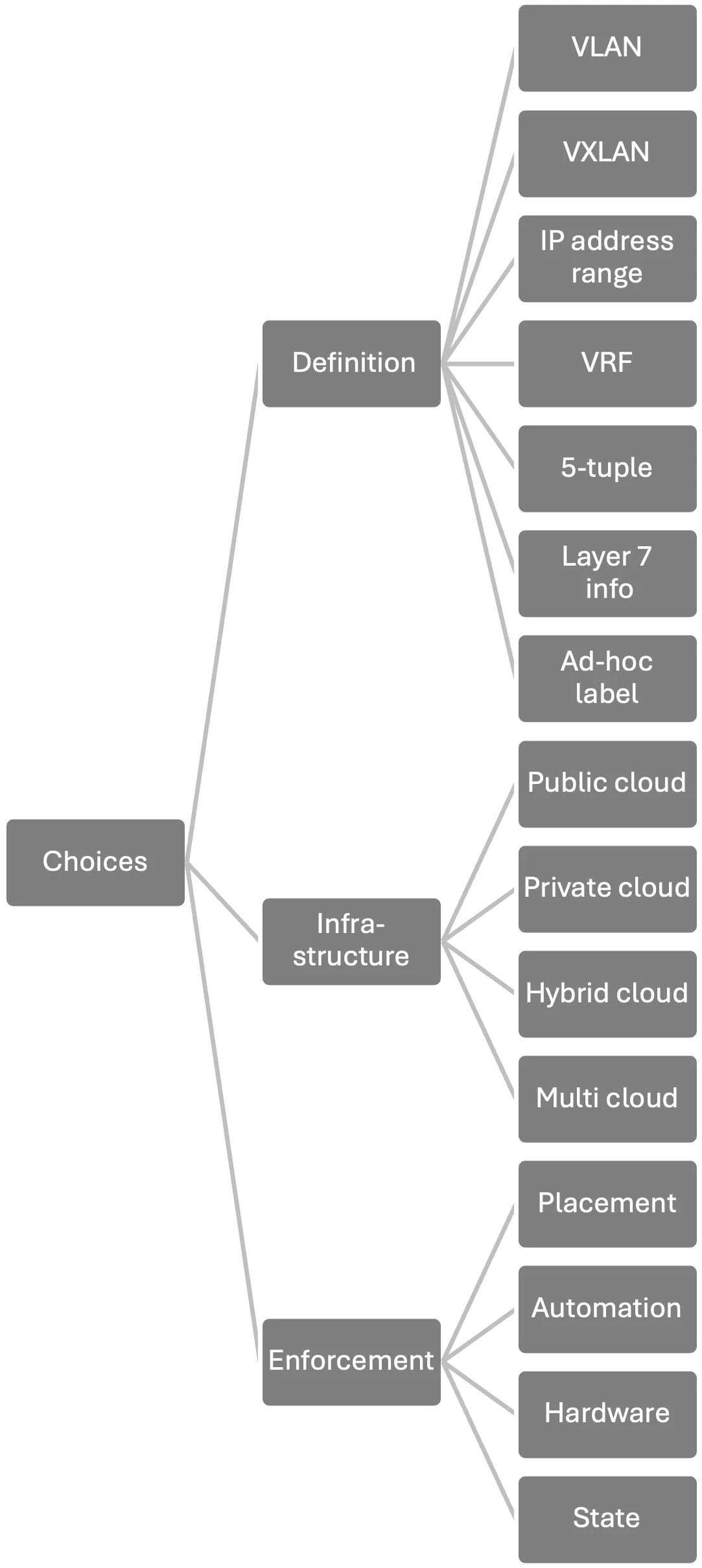
Given the speedy evolution of segmentation, its numerous sorts and using jargon by distributors, segmentation is in determined want of a longtime taxonomy. Thankfully, the TechRxiv paper does an incredible job of organizing segmentation taxonomy, separating phrases into three buckets:
- How Segments are Delineated: The way in which segments are outlined is a essential differentiation between segmentation sorts. For instance, utilizing VLAN IDs is taken into account macro-segmentation as every VLAN acts as its personal broadcast area. Utilizing 5-Tuples-based segments (the supply and vacation spot IP addresses, the supply and vacation spot port numbers and the protocol ID) works for each macro- and micro- segmentation.
- The Infrastructure Over Which Segmentation is Deployed: Segmentation additionally differs based mostly on the underlying infrastructure. This consists of public cloud, personal cloud, hybrid cloud and multi-cloud environments.
- How Enforcement is Applied: The way in which segmentation is enforced additionally gives essential differentiation of segmentation sorts. Allowing and blocking visitors could be executed on the workload stage (container community interface), near it (top-of-rack switches) or away from it (information heart firewall).
Offering Clients with Readability
Segmentation has developed right into a essential safety instrument that enables enterprises to isolate particular workloads based mostly on habits or identification – offering a strong basis for zero belief methods. Nonetheless, segmentation is a extremely fragmented market with quite a few methods to outline segments throughout a number of infrastructures with various enforcement strategies. Matching the suitable instrument to every job would require all stakeholders to return collectively to agree on an ordinary taxonomy for the know-how. Solely then will organizations achieve the readability they should align their segmentation initiatives with enterprise targets.
I sit up for offering extra content material round segmentation in future posts. Within the meantime, take a learn of the TechRxiv paper.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media

