Further Contributor: Apaar Sanghi
Cisco Safe Firewall (CSF) is persistently including new options and integrations, with many current enhancements involving logging and Splunk. One space of integration between CSF and Splunk that we labored on at Cisco Dwell Melbourne concerned Enterprise Safety Content material Replace (ESCU) detections in Splunk Enterprise Safety (ES). On this weblog submit we’ll check out what Splunk ESCU detections are, some modifications we made to get these detections to work with our SOC logging configuration, and have a look at an instance of how we used these ESCU detections in our SOC workflows.
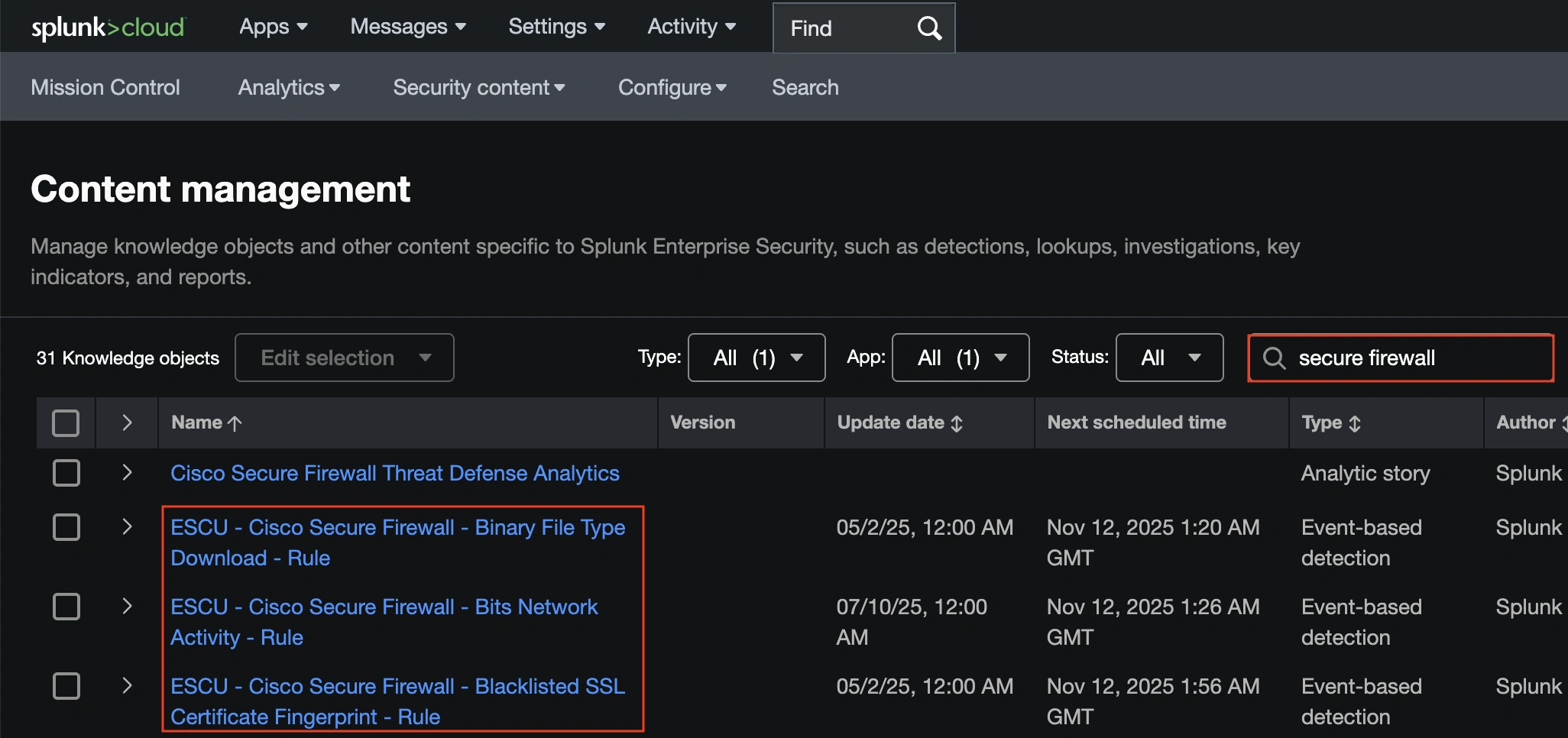
Splunk ES has round two dozen ESCU detections for Cisco Safe Firewall. These may be accessed from ES by navigating to Safety Content material > Content material Management after which looking for ‘Safe Firewall’.
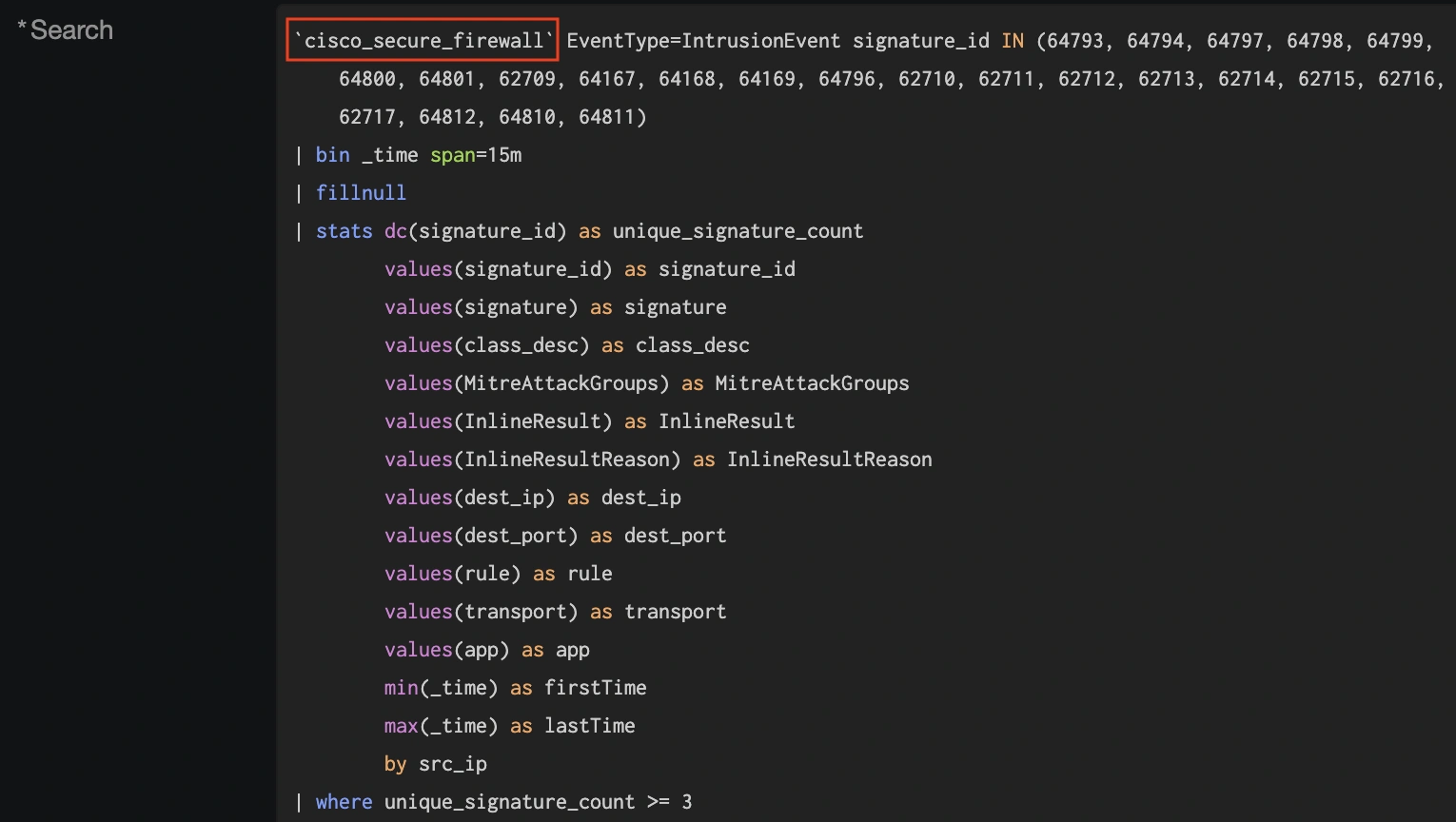
All ESCU detections for Safe Firewall reference the identical macro, ‘cisco_secure_firewall’.
The default configuration for this macro references the eStreamer shopper, which is frequent for information ingest from CSF. Nevertheless, Cisco now recommends syslog for brand spanking new deployments, as syslog can ship higher ingest efficiency over eStreamer, and plenty of enhancements to syslog output are included in our 10.0 launch and street mapped for future releases.
Within the Cisco SOC, we attempt to keep on the chopping fringe of configuration in order that we will check new options, detections, and integrations. We transitioned our firewall log export to syslog just a few conferences in the past, and in Melbourne we determined to check the ESCU detections with syslog.
There are just a few methods we will do that.
- We are able to modify the present ESCU detections to level to a brand new macro.
- We are able to clone the present ESCU detections and set a brand new macro on the clones.
- we will depart the entire ESCU detections alone and easily change the underlying macro they reference.
We opted for possibility 3 (although we did additionally do some customization by way of cloning). This required altering the macro pictured above by navigating to Settings > Superior Search after which clicking ‘Search macros’.
Trying to find the macro from the ESCU detections will present the Definition is ready to sourcetype=”cisco:sfw:streamer”.
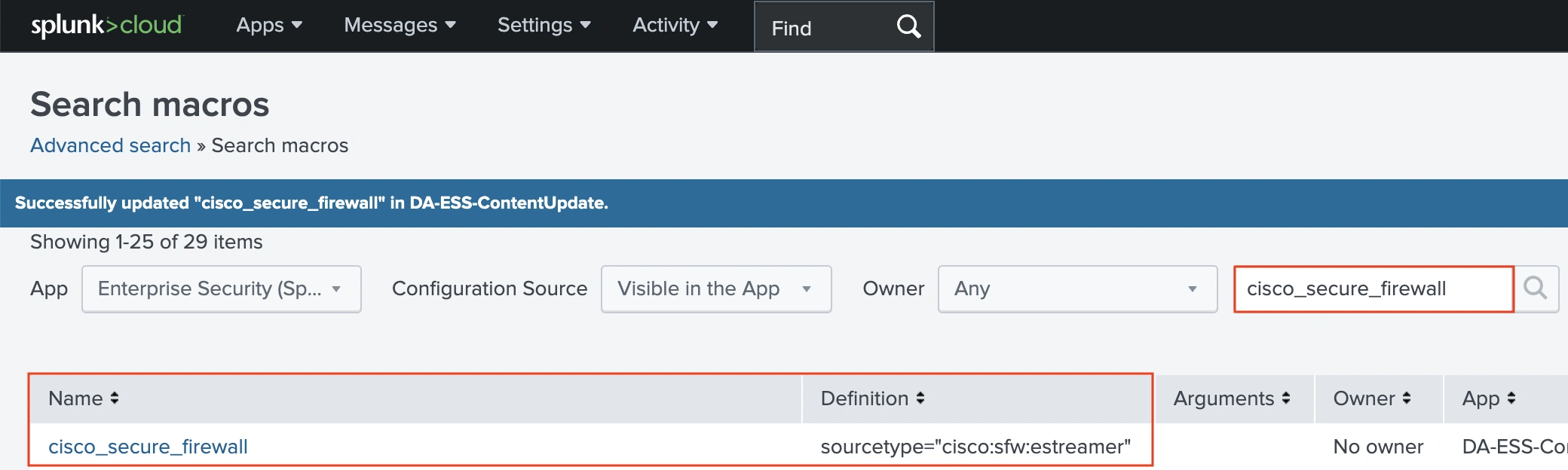
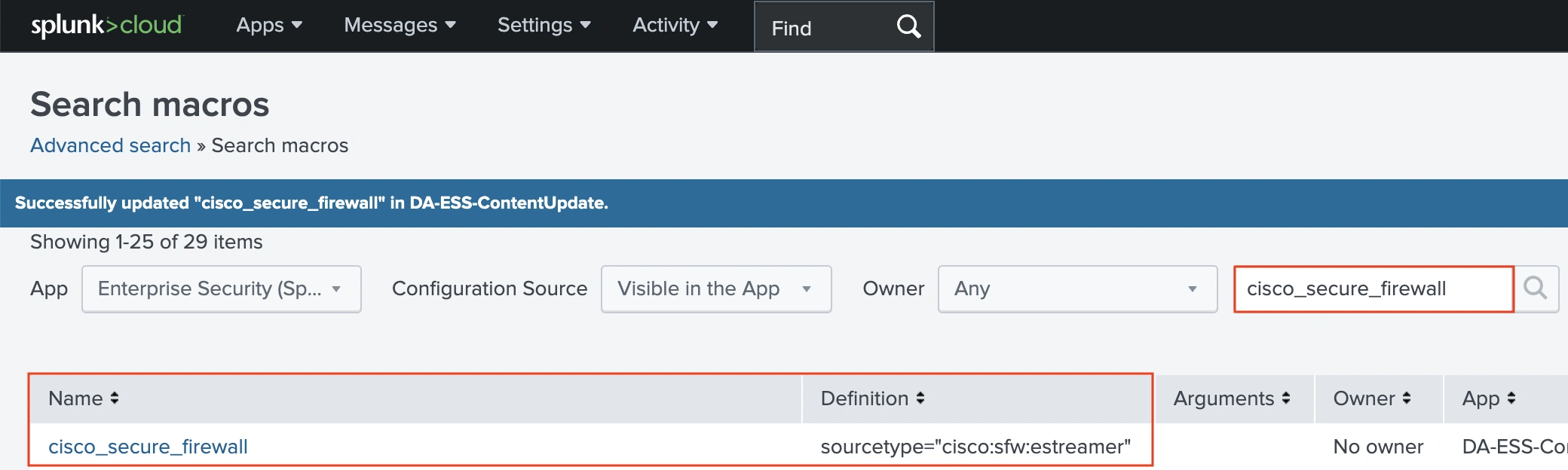
We are able to substitute this with the sourcetype for our syslog, and we additionally must outline the index for our syslog. For the Melbourne SOC, our index is se_network_ftd.
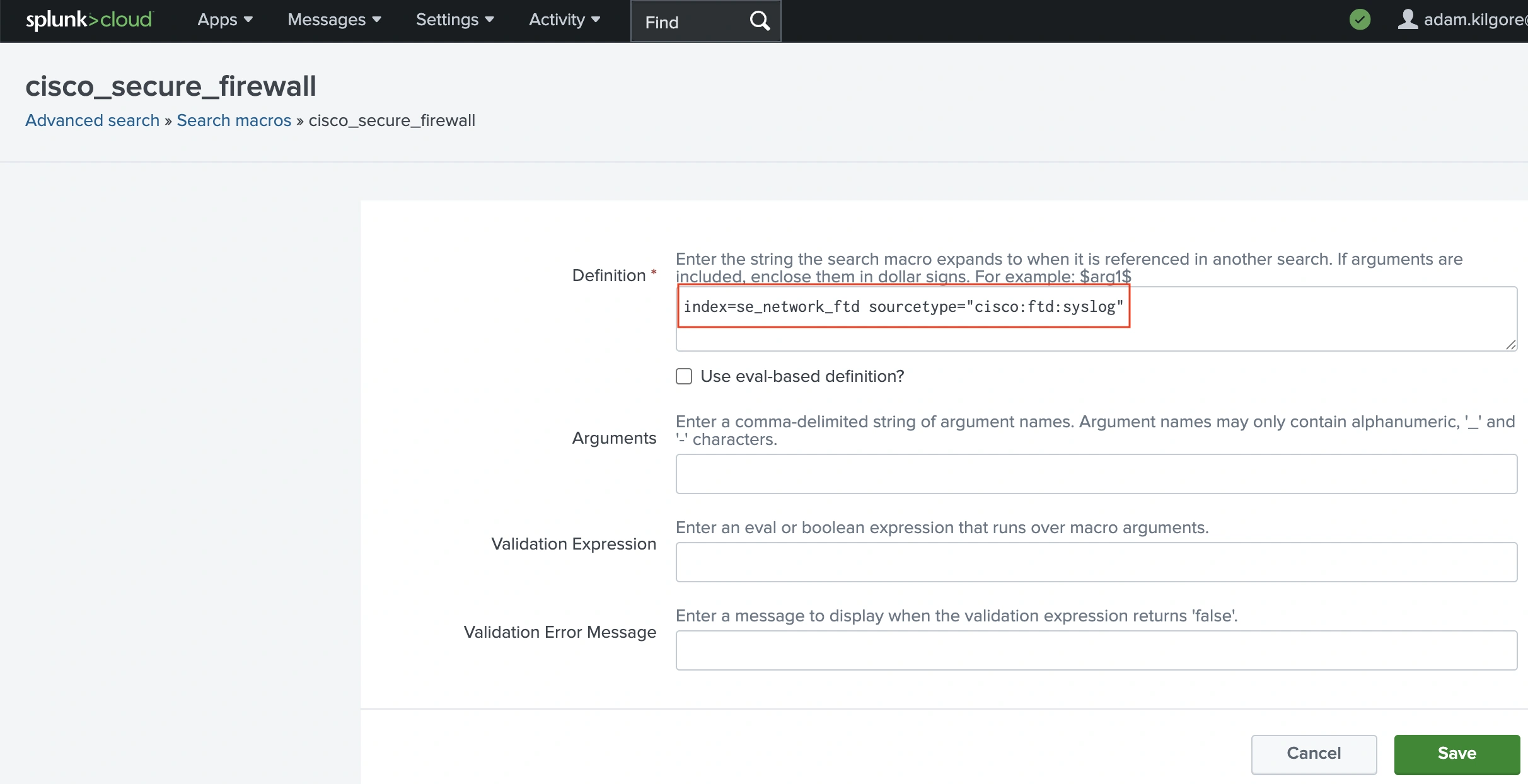
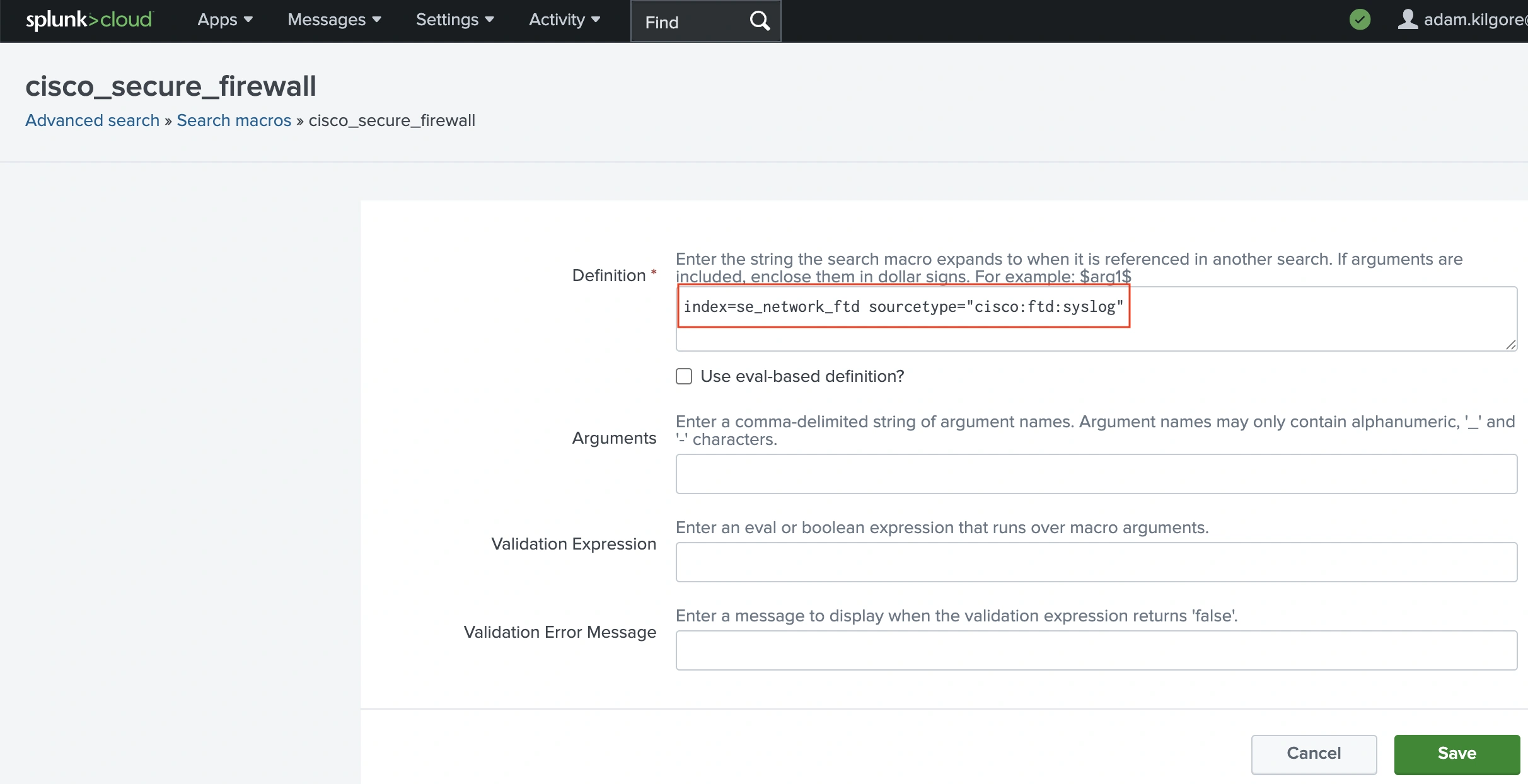
With this setting, the macro utilized by the entire Safe Firewall ESCU detections will now level on the index and sourcetype for our syslog occasions. The searches related to the ESCU detections will nonetheless work after switching from eStreamer to syslog as a result of the Cisco Safety TA makes use of Splunk’s schema-on-read method to provide the identical occasion schema throughout question for each eStreamer and syslog occasions.
Word: for organizations transitioning from eStreamer to syslog, the macro may be configured to drag from both eStreamer or syslog through the use of an ‘or’ situation. For our index, this may appear to be the next:
index=se_network_ftd AND (sourcetype=cisco:ftd:estreamer OR
sourcetype=cisco:ftd:syslog)Within the SOC we don’t decrypt attendee visitors on goal, so Encrypted Visibility Engine (EVE) occasions are extremely useful as an Indicator of Compromise (IoC). One of many Splunk ESCU detections that we used entails EVE occasions instantly.


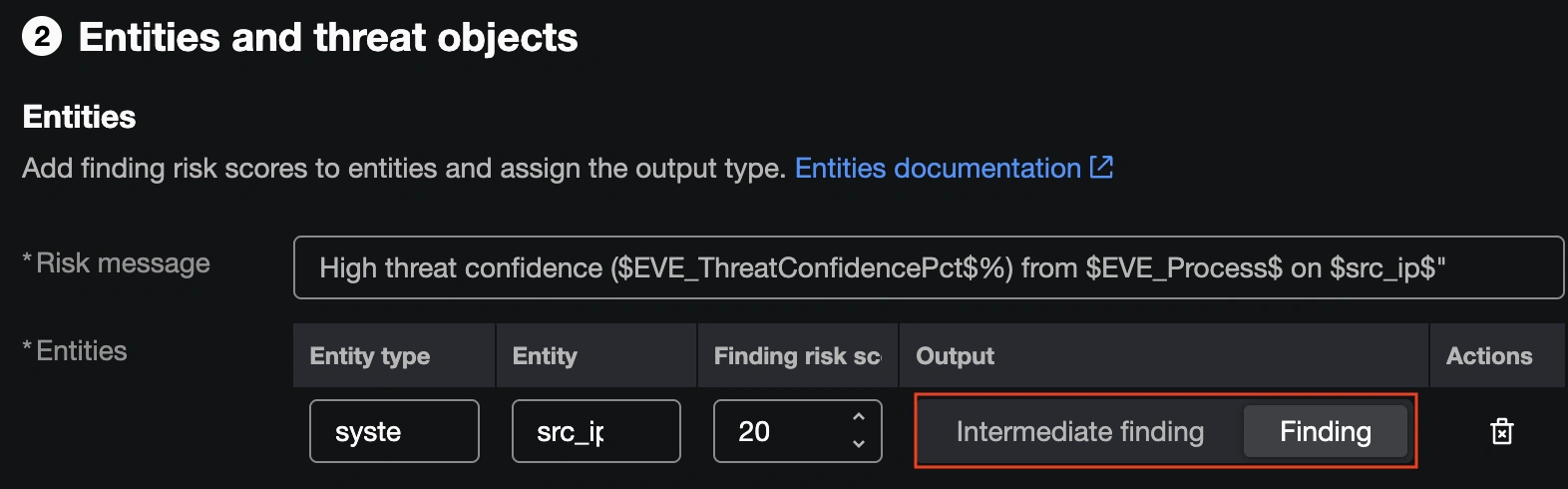
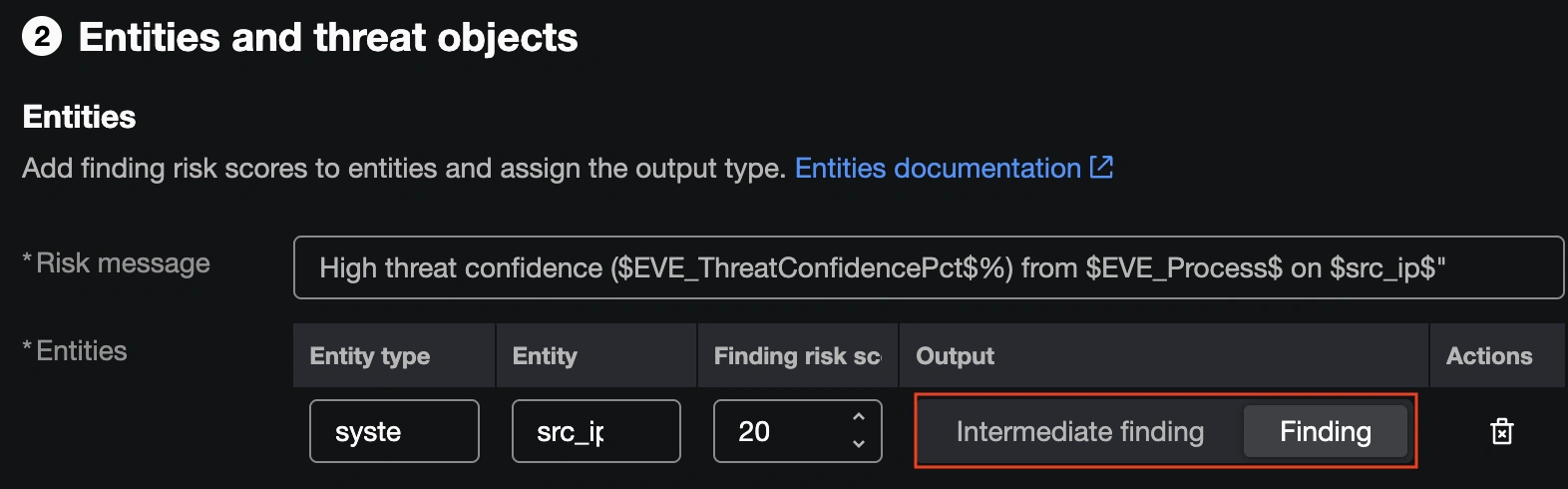
By default, this ESCU detection will match on a Safe Firewall connection occasion with EVE risk confidence above 80. Nevertheless, this detection will use the EVE occasion as an Intermediate Discovering, which raises the danger score of the concerned supply IP with out producing a full incident.
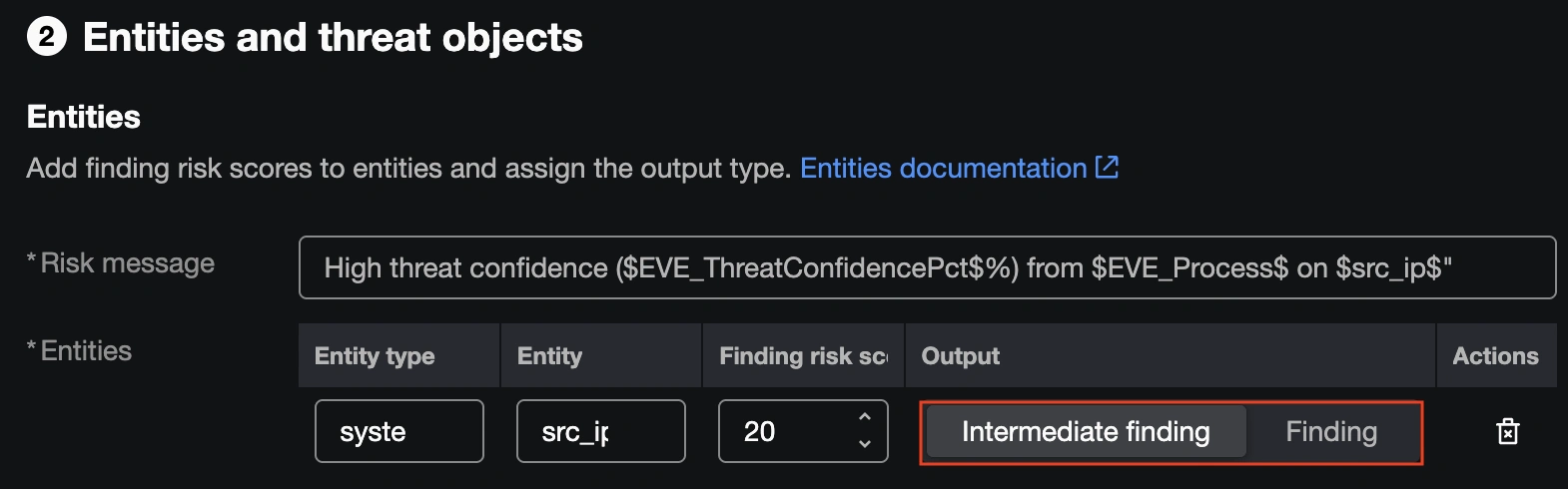
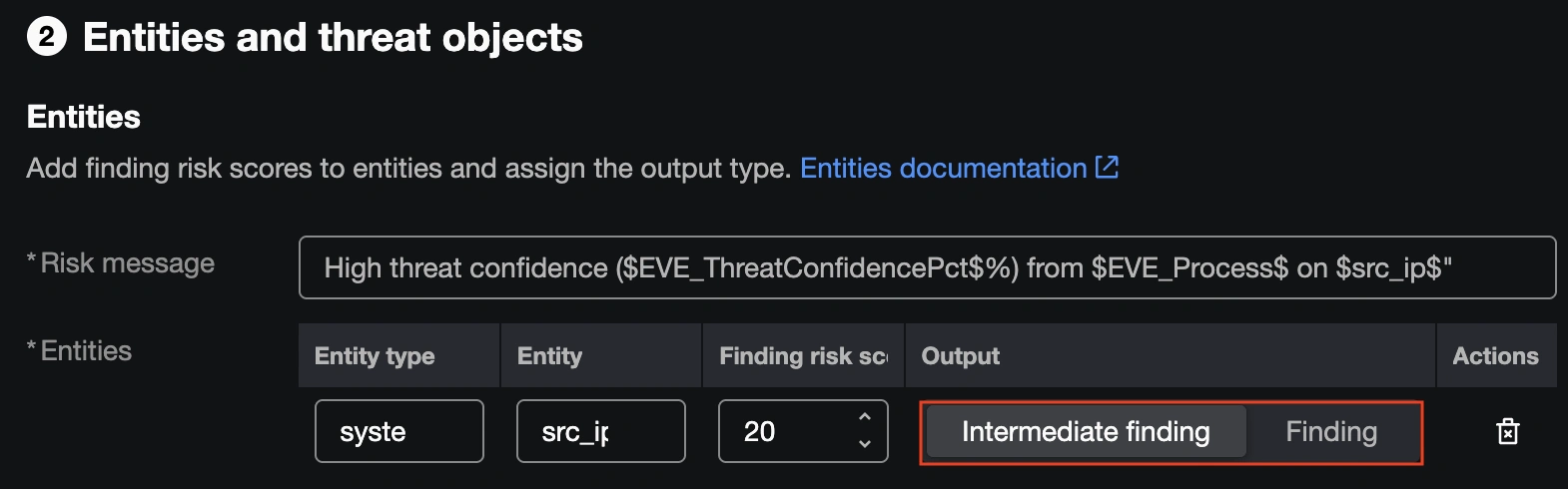
This would be the proper name for a lot of environments, however on the SOC we now have a low sufficient quantity of excessive confidence EVE occasions and place sufficient worth on them to warrant selling them to full incidents. We opted to alter the setting to Discovering, so {that a} single Safe Firewall connection occasion with a excessive EVE risk confidence rating will generate a Discovering by itself.
With the Discovering setting in place, all excessive confidence EVE occasions have been mechanically promoted to Incidents in Splunk ES, making certain we noticed them shortly and will reply with an investigation.
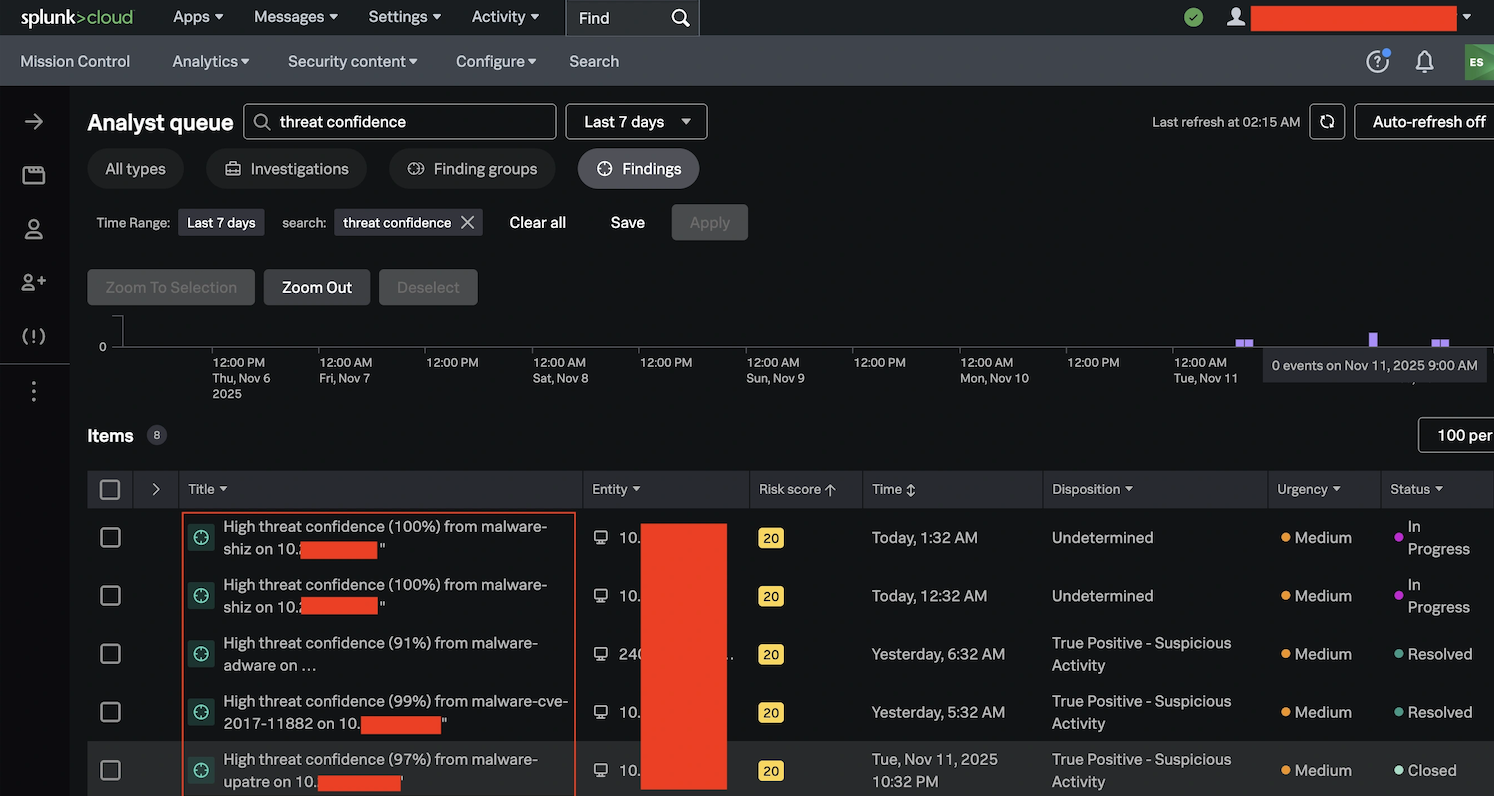
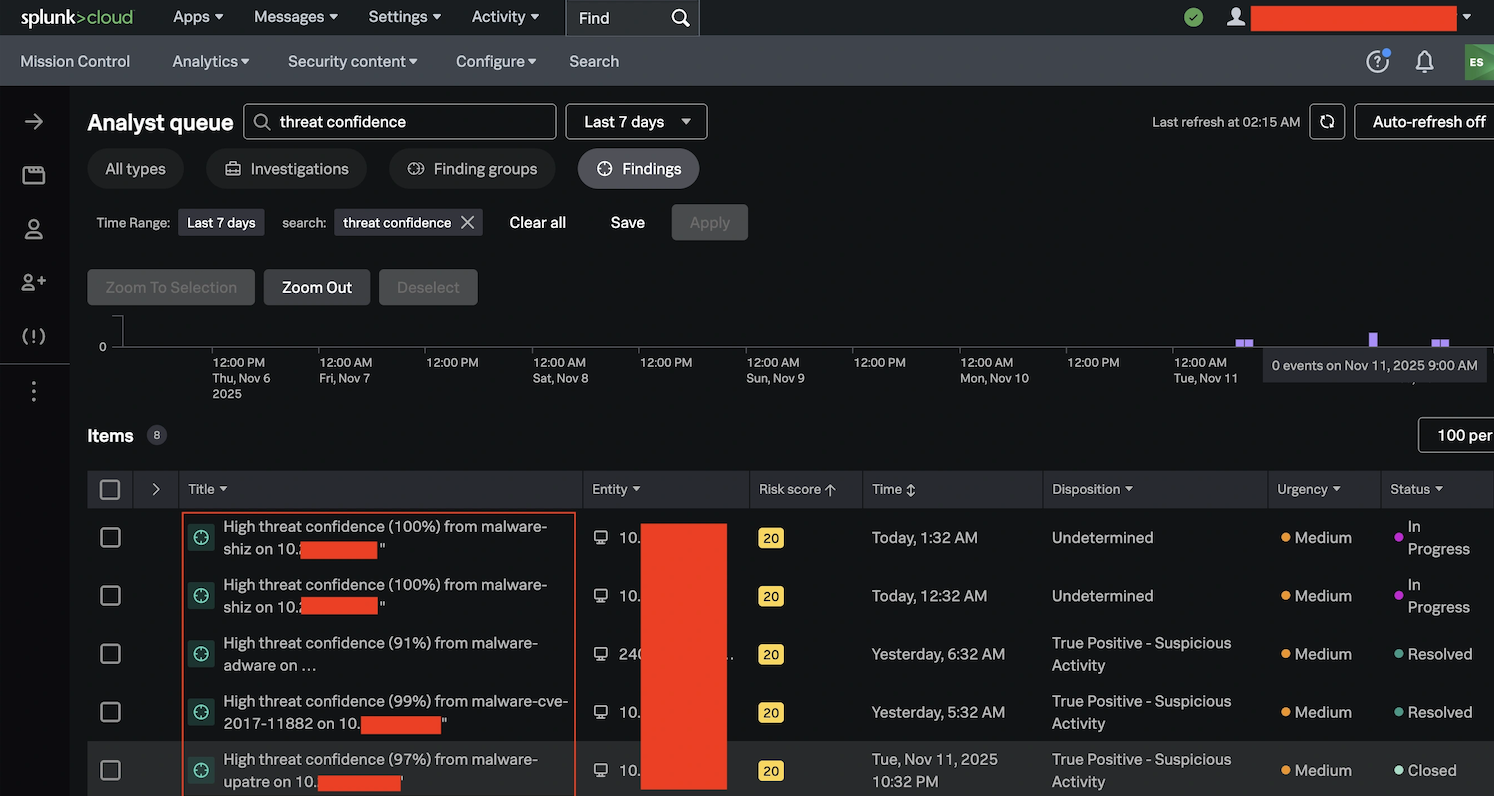
Whereas we run numerous our incident investigations by Cisco XDR on the SOC, the convenience of use of this workflow and the Splunk ESCU detection capabilities proved to be a useful software that we are going to broaden at future conferences.
Try the opposite blogs by my colleagues within the Cisco Dwell APJC 2026 SOC.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media

