Barcelona is a metropolis of marvel, outlined by the architectural genius of Antoni Gaudí. For the 100,000+ attendees of the Cell World Congress 2026, these landmarks had been must-see locations. However the place there may be excessive curiosity, there may be excessive alternative for cybercriminals.
This was a part of the backdrop for our mission in early March. As essentially the most influential mobility and networking occasion on the planet, MWC 2026 was a whirlwind of innovation. On the heart of this high-stakes surroundings, our staff was on the bottom, working the Safety and Community Operations Heart (S/NOC) to make sure that the large infrastructure powering the occasion remained bulletproof, and the attendees utilizing its community had been safe.


Our SOC was based mostly on cutting-edge applied sciences offered by Cisco, consisting of the just lately launched AI prepared ultra-high-end Safe Firewall 6160, our main Safety Service Edge resolution Cisco Safe Entry , our AI safety resolution Cisco AI Protection, our premium SIEM resolution Splunk Enterprise Safetyand our cloud-native detection and response resolution Cisco XDR.
Safe Entry
As a result of nature of the occasion, we had been solely utilizing the DNS capabilities of Safe Entry, additionally accessible within the Safe Entry DNS Protection resolution, with safety utilized on the DNS stage. The DNS queries of the linked units had been forwarded to the Safe Entry public resolvers the place we block threats earlier than a connection is established. All the safety occasion logs had been pushed on to XDR, whereas Splunk ES was pulling all of the anonymised logs, and AI Protection was gathering App Discovery logs for Generative AI purposes to present further insights of the AI fashions used on the community of the occasion.
Splunk Platform


Within the picture above, you’ll be able to see a customized dashboard we created on Splunk ES consuming all of the logs it was receiving from the Firepower Risk Protection 6160 firewall, and the DNS requests despatched to the Safe Entry public resolvers. On this particular screenshot, we’re exhibiting the info for the final seven days from the afternoon of the final day of the occasion, the 5th of March (as an alternative of the final 24 hours showing on the titles of the graphs, which was what we had been usually observing).
Please word that the community of the venue stays protected on the DNS stage by Cisco Safe Entry exterior the occasion. In consequence, there are DNS logs exterior the dates of the MWC, because the community was actively used throughout the setup.
XDR
Within the customised XDR dashboard beneath, you’ll be able to see some high-level data extracted from the DNS site visitors of the community. This contains the whole variety of DNS requests for the final 30 days, and the blocks for Malware, Command and Management, and Phishing for a similar interval.
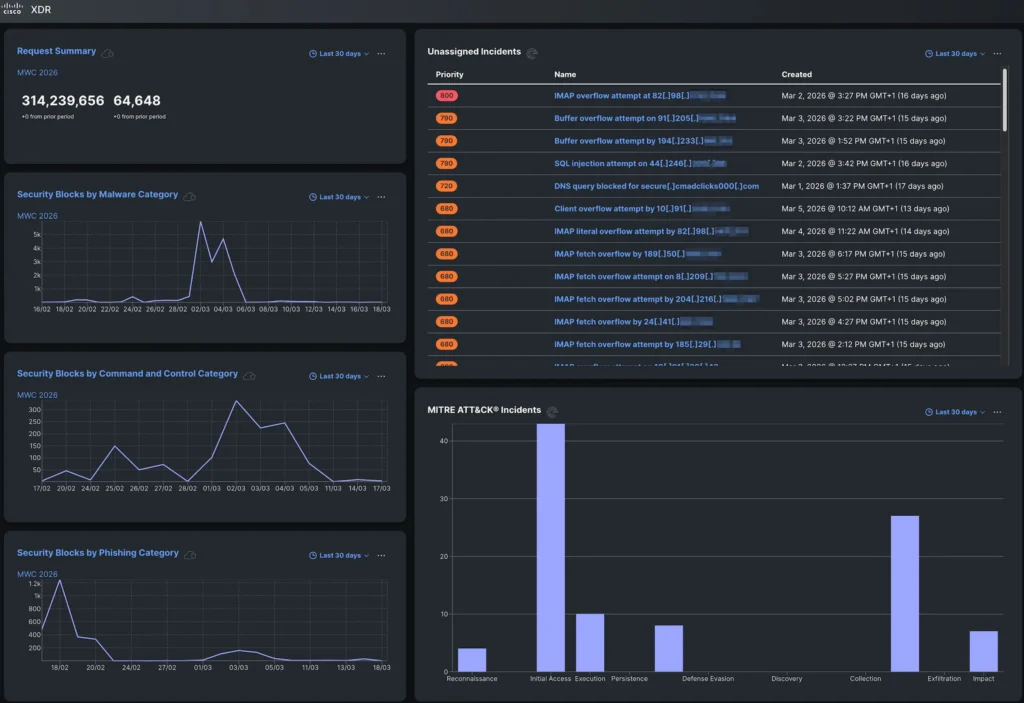
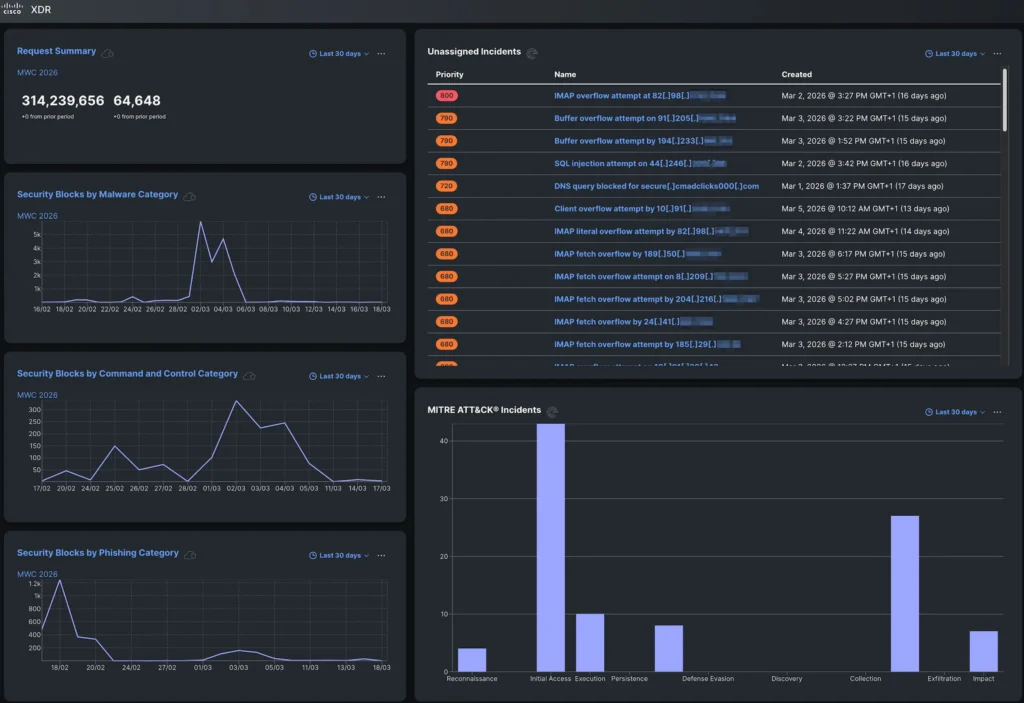
There are once more occasions exterior the dates of the MWC. It’s price noting {that a} phishing marketing campaign seems to have taken place on the venue throughout a earlier occasion in mid-February.
On the right-hand aspect, you’ll be able to see incidents that had been robotically created on XDR after correlating the DNS logs from Safe Entry and the firewall logs from the FTD 6160, and MITRE ATT&CK Incidents.
AI Protection
Whereas Generative AI is a strong device, it imposes vital dangers that organisations want to concentrate on and handle accordingly. In the picture beneath, you’ll be able to see an App Discovery report from AI Protection exhibiting the AI purposes found on the community of the venue. The Composite Danger Rating happens by combining Enterprise Danger, Utilization Danger, and Vendor Compliance to calculate a standardised measure of the danger they might suggest.
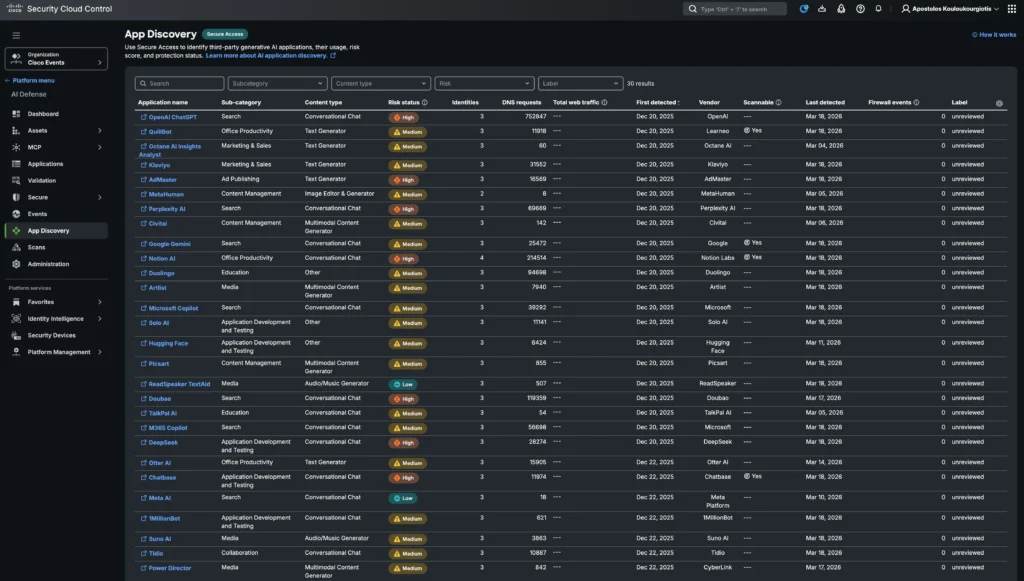
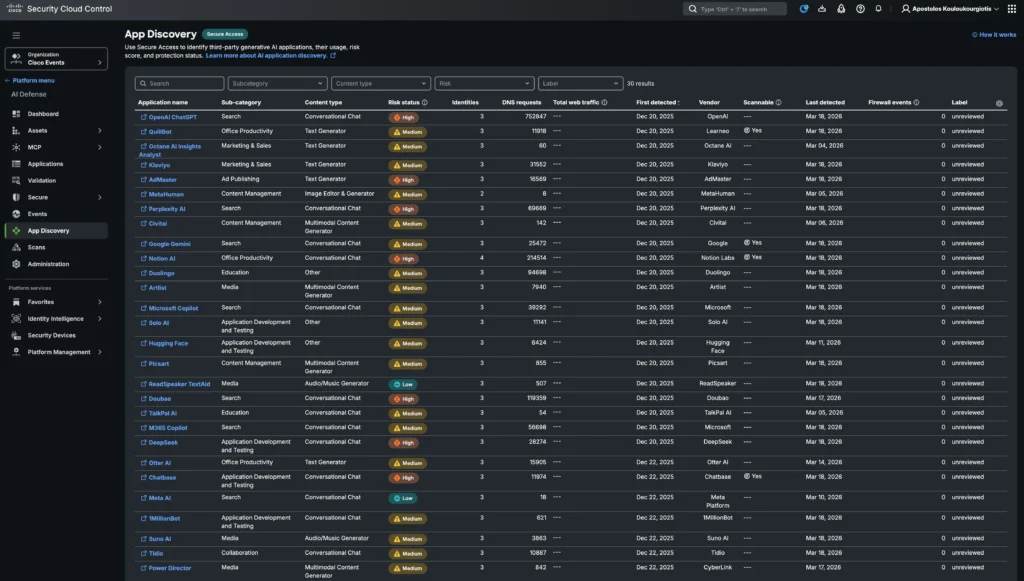
Entry to those AI fashions could be managed with Safe Entry to safe AI aside from simply leveraging AI for safety. In a non-anonymised surroundings the place the site visitors is routed by the Safety Service Edge (SSE)’s cloud-hosted Safe Net Gateway, the purposes could be scanned to implement AI guardrails by the Safe Entry DLP (knowledge loss prevention) coverage and management what knowledge is distributed to the AI purposes, whereas tenant controls may also be utilized.
When the guard is down
Whereas attendees had been busy planning their sightseeing exterior the occasion, attackers had been busy crafting traps. We noticed a surge in subtle phishing campaigns concentrating on the very folks attending the convention. Fraudsters stood up convincing, pretend web sites completely mimicking official ticket portals for town’s prime points of interest, designed to reap bank card particulars and drain accounts earlier than the victims even reached the entrance doorways of the breath-taking Basílica de la Sagrada Família on this instance.
It was a stark reminder: even essentially the most seasoned tech consultants who spend their careers constructing defenses and searching threats could go away a digital door unlatched after they step away from work. The identical AI-powered vigilance we apply to international enterprise networks is simply as essential in our private digital lives. At MWC 2026, we weren’t simply monitoring the community; we had been witnessing a masterclass in how shortly a second of leisure can flip into fraud.
Through the occasion, Safe Entry blocked entry to a kind of phishing domains.
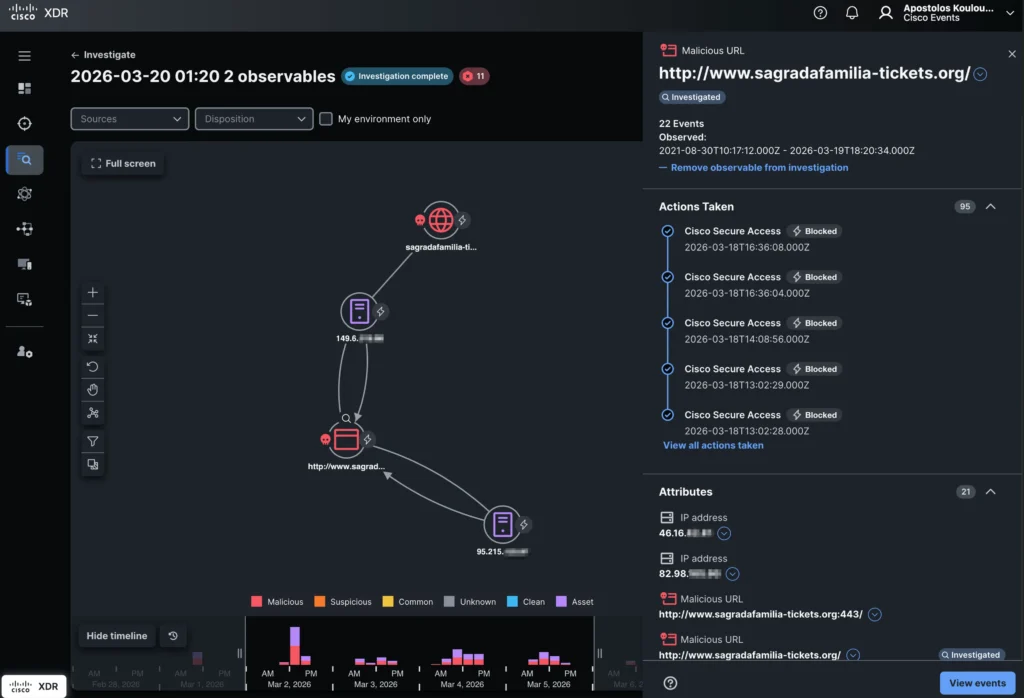
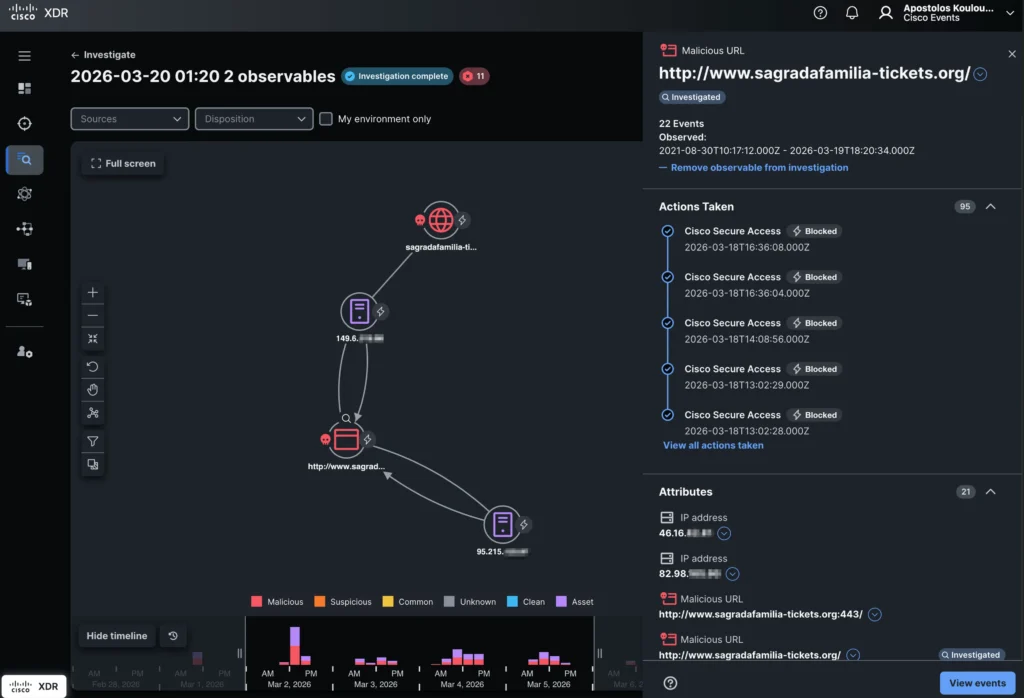
Whereas Safe Entry was implementing solely on the area stage, with XDR Examine we might correlate logs from each Safe Entry and the FTD 6160 firewall to offer additional data, like the precise URLs customers tried to entry, showing as Attributes on the right-hand backside of the picture above.
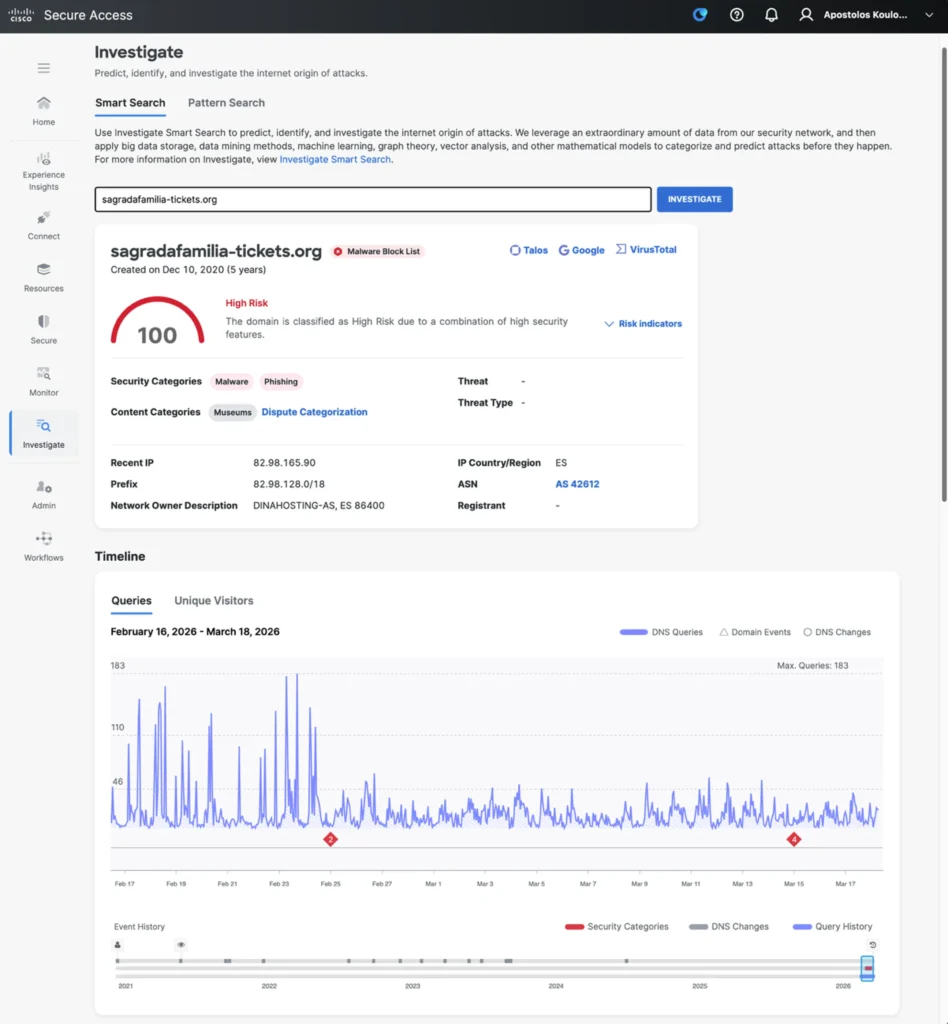
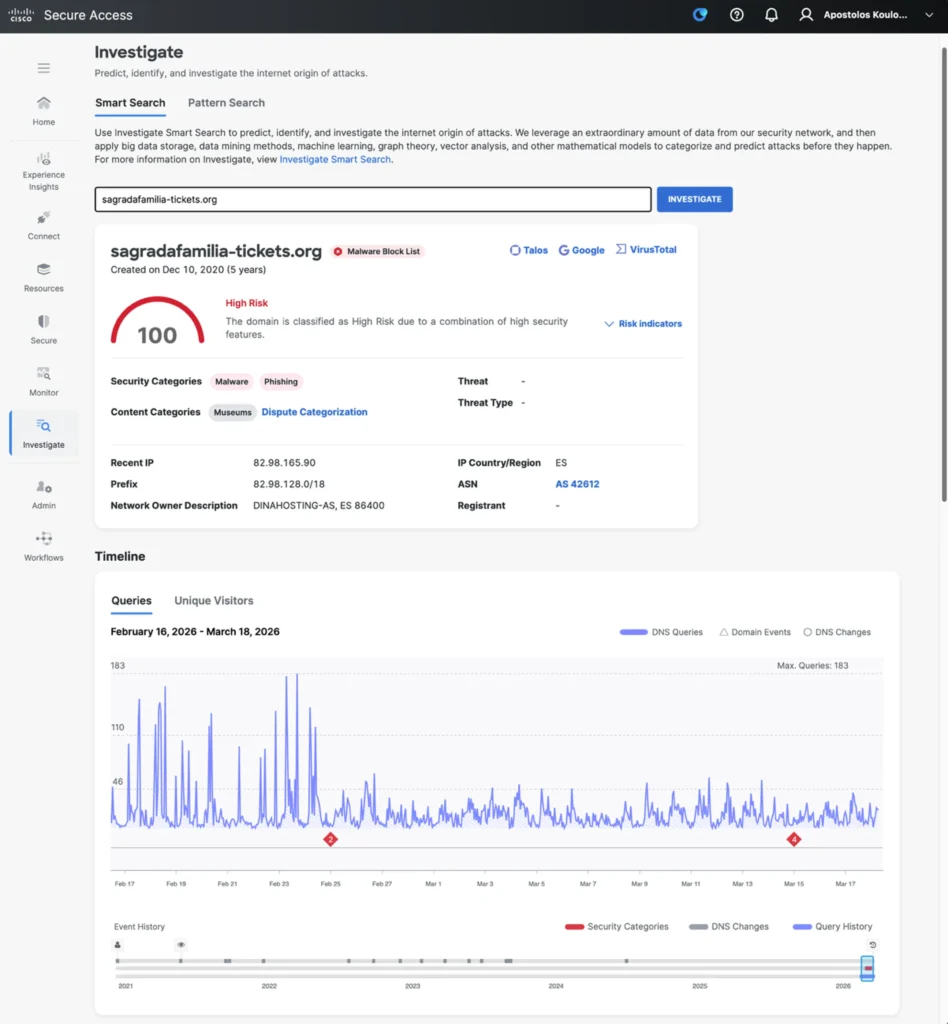
Safe Entry Examine, as showing above, offers real-time actionable menace intelligence by analysing international knowledge from the Safe Entry community utilizing AI to detect, rating, and predict rising threats. It permits safety groups to proactively uncover malicious infrastructure (domains, IPs, ASNs) and speed up incident investigation by API-driven, high-context knowledge enrichment.
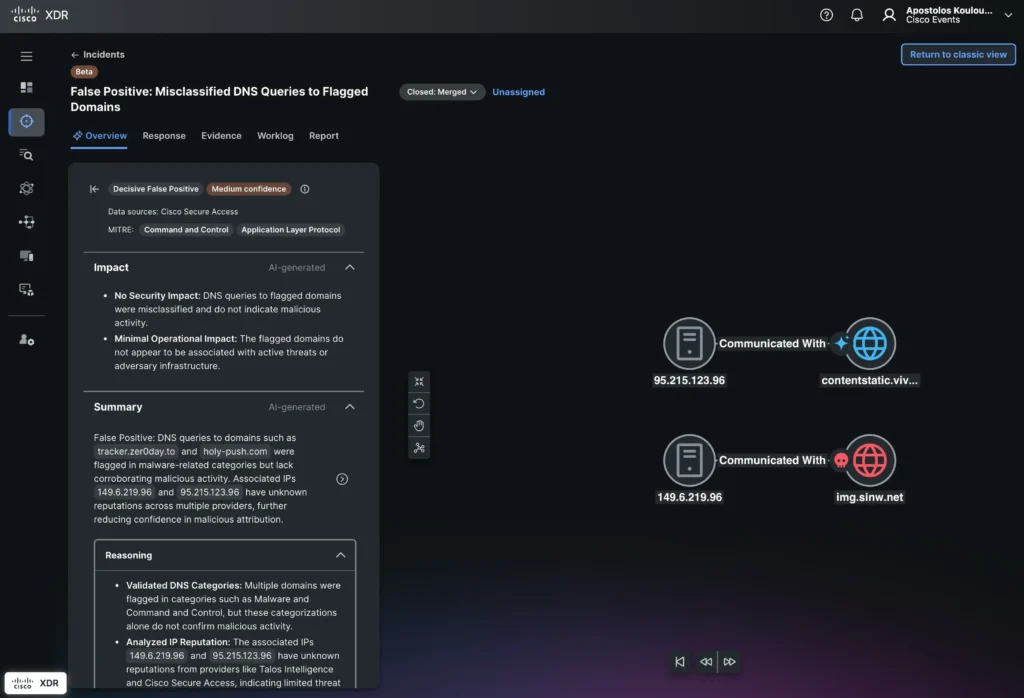
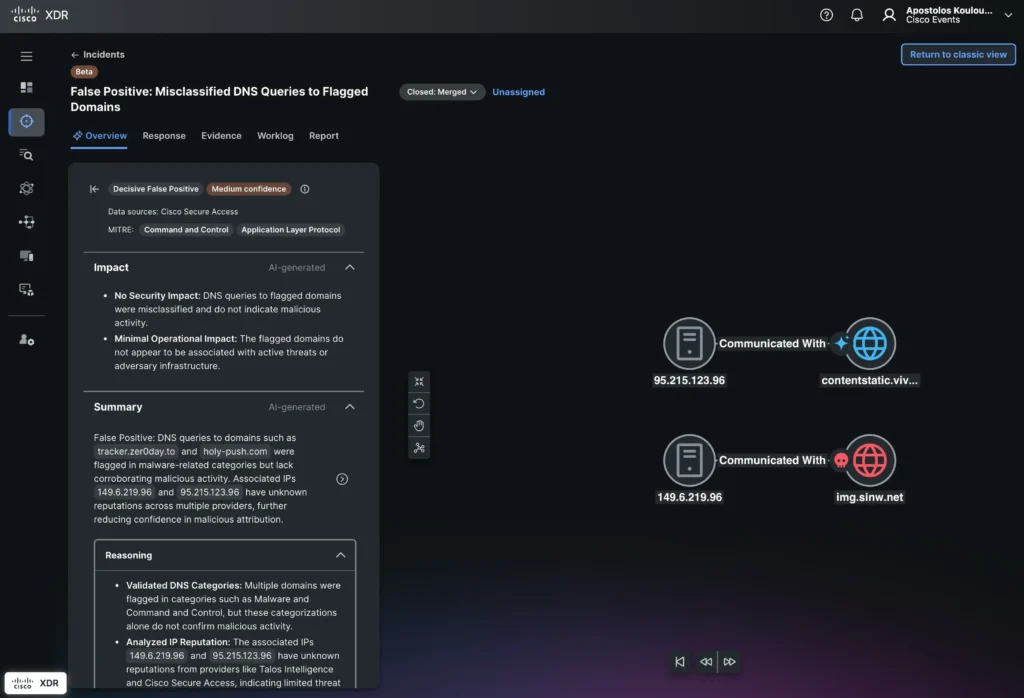
XDR can then correlate occasions additional to present extra Incidents which aren’t as apparent because the above phishing occasion. Its AI-powered incident evaluation (showing above) offers AI-generated Classification, Impression, and a Abstract together with the Reasoning, Proof and Detections for each incident. The further AI-generated Evaluation and Suggestions are invaluable for the integrations with Safe Entry and Splunk ES to automate responses for each incident, whereas they facilitate escalations to senior safety analysts when additional guide motion is required. On this particular case, XDR labeled this incident as a possible false optimistic with medium confidence. Primarily based on that, the SOC staff can prioritise different incidents of upper precedence.
Concluding
The AI-powered Safety and Community Operations Heart (S/NOC) at Cell World Congress 2026 demonstrated Cisco’s dedication to leveraging cutting-edge applied sciences to safe and optimise large-scale, high-profile occasions. By integrating superior options such because the AI-ready Safe Firewall 6160, Cisco Safe Entry, Cisco AI Protection, Splunk Enterprise Safety, and Cisco XDR working all collectively as a single platform, the S/NOC offered complete, multi-layered safety that proactively blocked threats, together with phishing campaigns, and delivered actionable insights by AI-driven analytics and correlation.
This deployment highlighted the facility of mixing AI, automation, and unified safety telemetry to reinforce menace detection, investigation, and response in actual time, whereas additionally enabling granular management over AI utility utilization. The occasion underscored the significance of a holistic, AI-enabled safety structure that not solely protects essential infrastructure but in addition educates and innovates to remain forward of evolving threats in advanced environments with various consumer populations.
Try the classes discovered from the Occasion SOCs we deploy world wide, with the white paper and newest blogs.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media

